Buffer Overflow Lab.docx - Buffer Overflow Lab Based heavily on a lab developed by Wenliang Du of Syracuse University as part of the SEED labs series | Course Hero

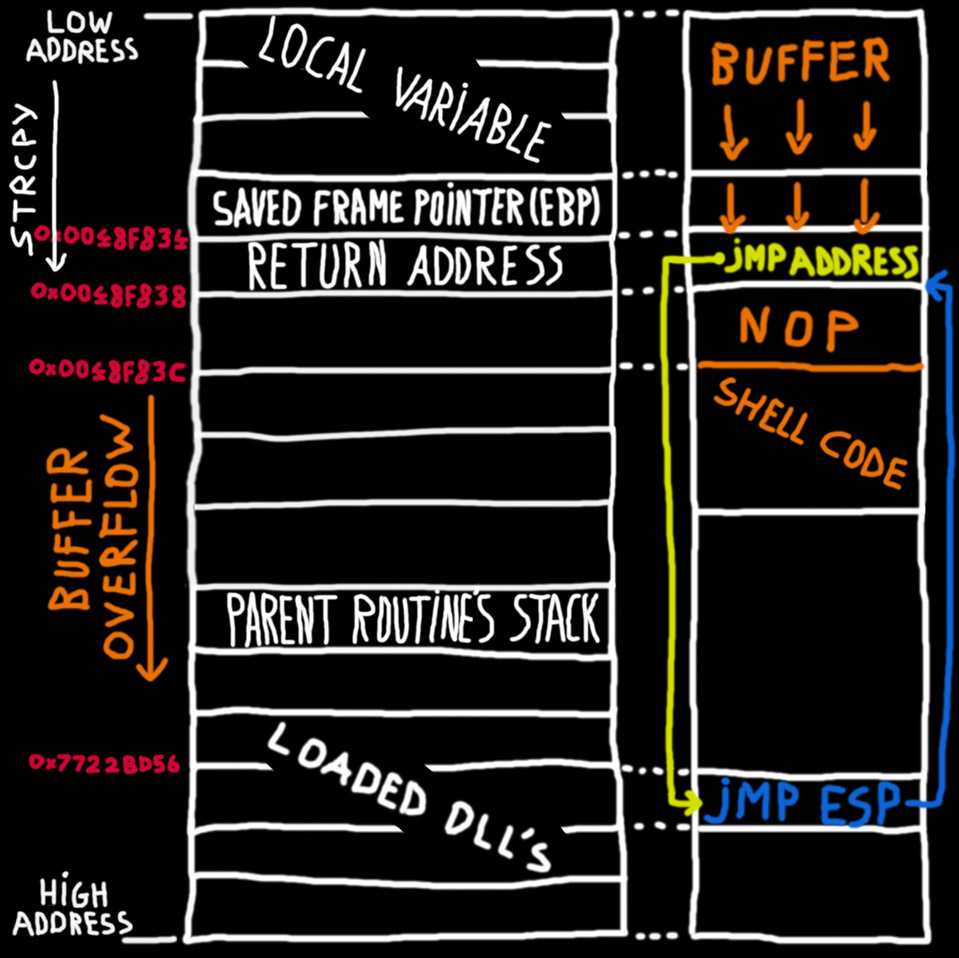
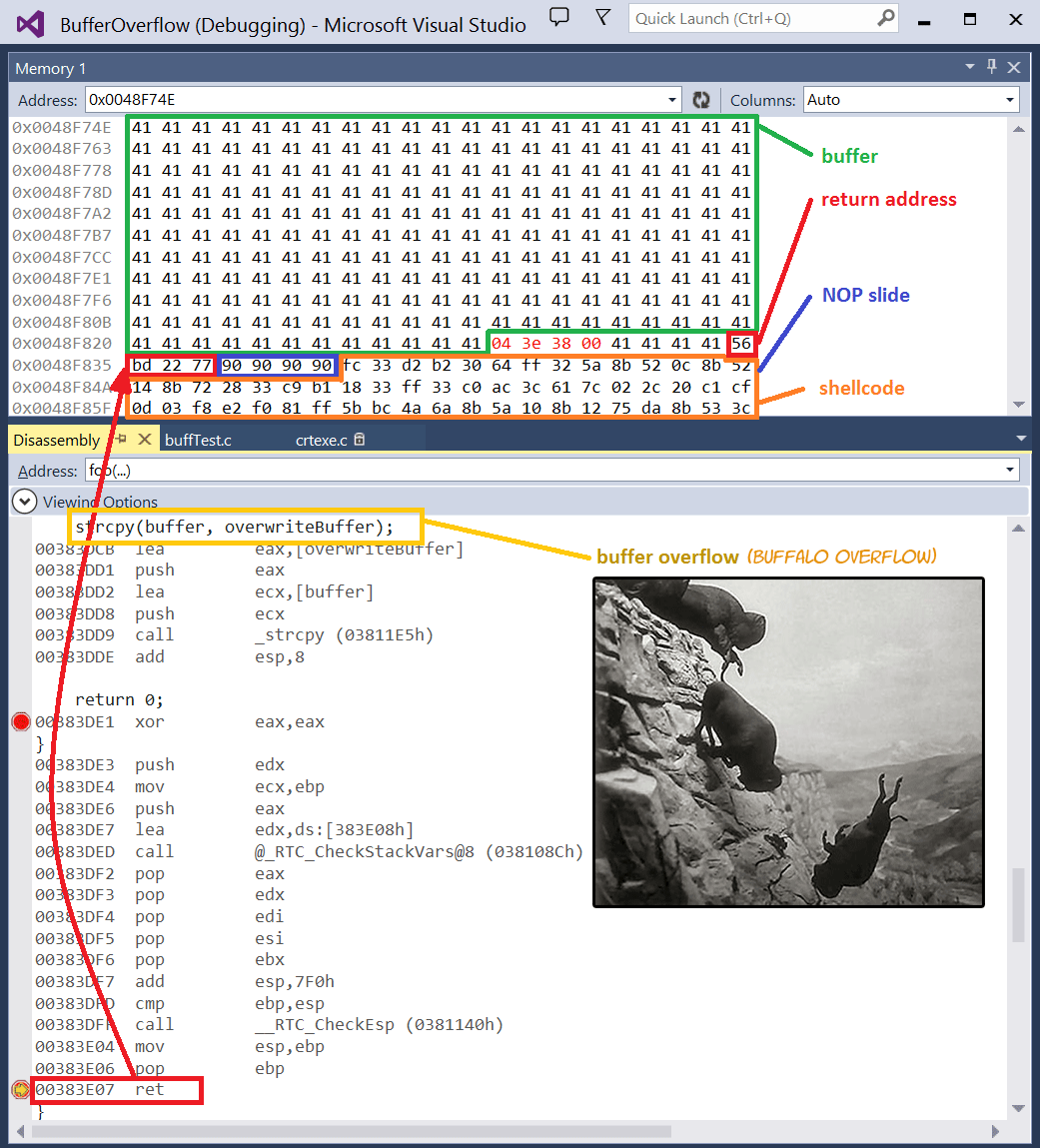
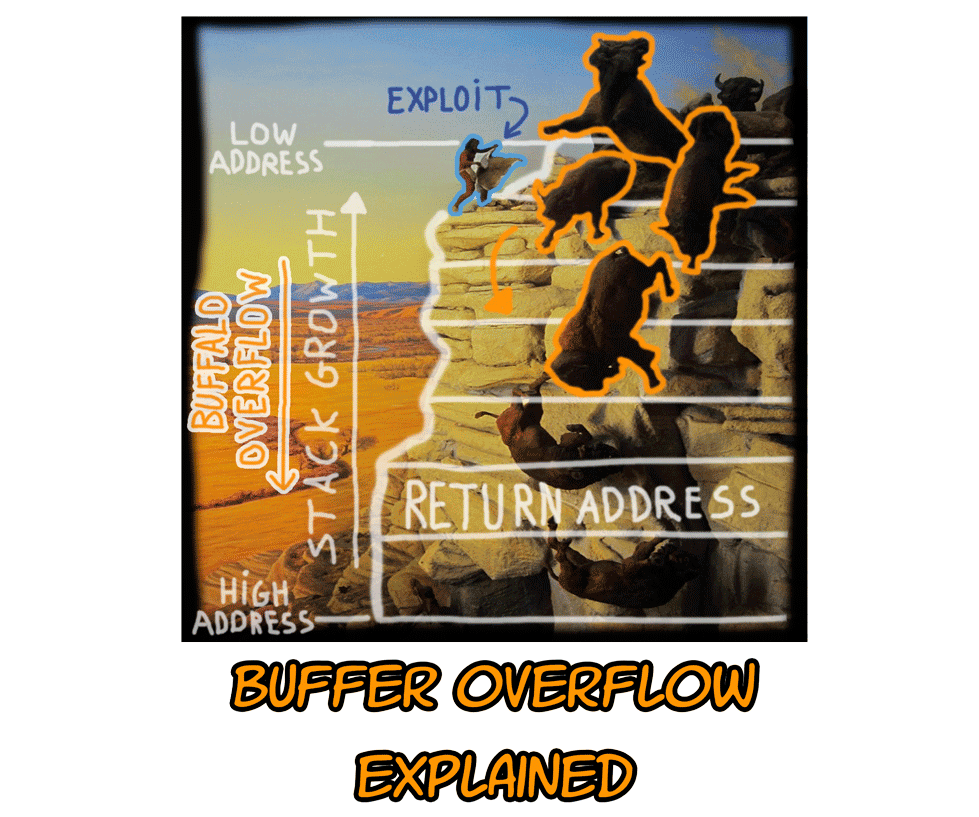
Lab 3 report.docx - Ankit Kumar 773312668 Buffer Overflow Vulnerability Lab Report Task 1: Non-root stack program Debug stack Figure 1.1 Return address | Course Hero

Overflow Conference (Buffalo) Recap | What a move of God we experienced in buffalo, New York! Thank you Curtis N Ani Minniefield and Sword of the Spirit Ministries for allowing us to
SUNY at Buffalo; Computer Science; CSE620 – Advanced Networking Concepts; Fall 2005; Instructor: Hung Q. Ngo 1 Agenda Last time: finished brief overview. - ppt download

swift - HKWorkoutRouteBuilder and CLLocationManager only adding route updates in increments - Stack Overflow